Yet another reason to switch to Firefox, or even better, a hardened fork like LibreWolf [email protected]
What functionality would I lose/gain if I switch from Firefox to Librewolf? I’m admittedly an amateur in the privacy space, and I’ve been pretty content with Firefox + Ublock and container tabs for different profiles, but I consistently get the issue that my browser fingerprint is pretty unique, and I have no idea how to or even if I can anonymize that anymore.
Librewolf is not associated with Mozilla and does not receive their primary source of funding from Google like Mozilla does. I really like having the same browser and browser synchronization between my phone and desktop/laptop, so librewolf is out for me. They have no interest or resources to build an Android version. Waterfox does at least have desktop / android option and takes things at least one small step further away from Google.
U can sync regular mobile ff and librewolf. Thats what i currently have.
It is the same browser. LibreWolf doesn’t change much of the Firefox code, mostly just the configuration. They enable various privacy/security settings by default and remove Mozilla telemetry. You can go to the LibreWolf settings and enable Firefox Sync, and it will work just fine with your Mozilla account and other Firefox browsers.
For Android, I like to use Mull, it’s a hardened build of Firefox, similar to LibreWolf.
Thanks for the answer! I run Windows, iOS and Linux across multiple devices, and sync is definitely needed for me as well. I’ll look into Waterfox!
The previous answer is misleading and partially just wrong. Firefox Sync works just fine in LibreWolf, you just need to enable it in the settings. I currently sync my LibreWolf browser on my Linux desktop to Firefox on iOS and Mull on Android, no issues whatsoever. The only Mozilla services that LibreWolf intentionally removes are their telemetry and Pocket.
You can enable Firefox sync in Librewolf, it works fine.
Tangent note: I think browser fingerprinting is only a source of concern if you use VPN. Otherwise, your IP is already a good enough identifier, and quite likely doesn’t rotate often enough. Please someone correct me if I’m wrong.
Yeah I’d only worry about it if I were trying to buy drugs on the dark net or something. I guess if torrenting became illegal I would also worry.
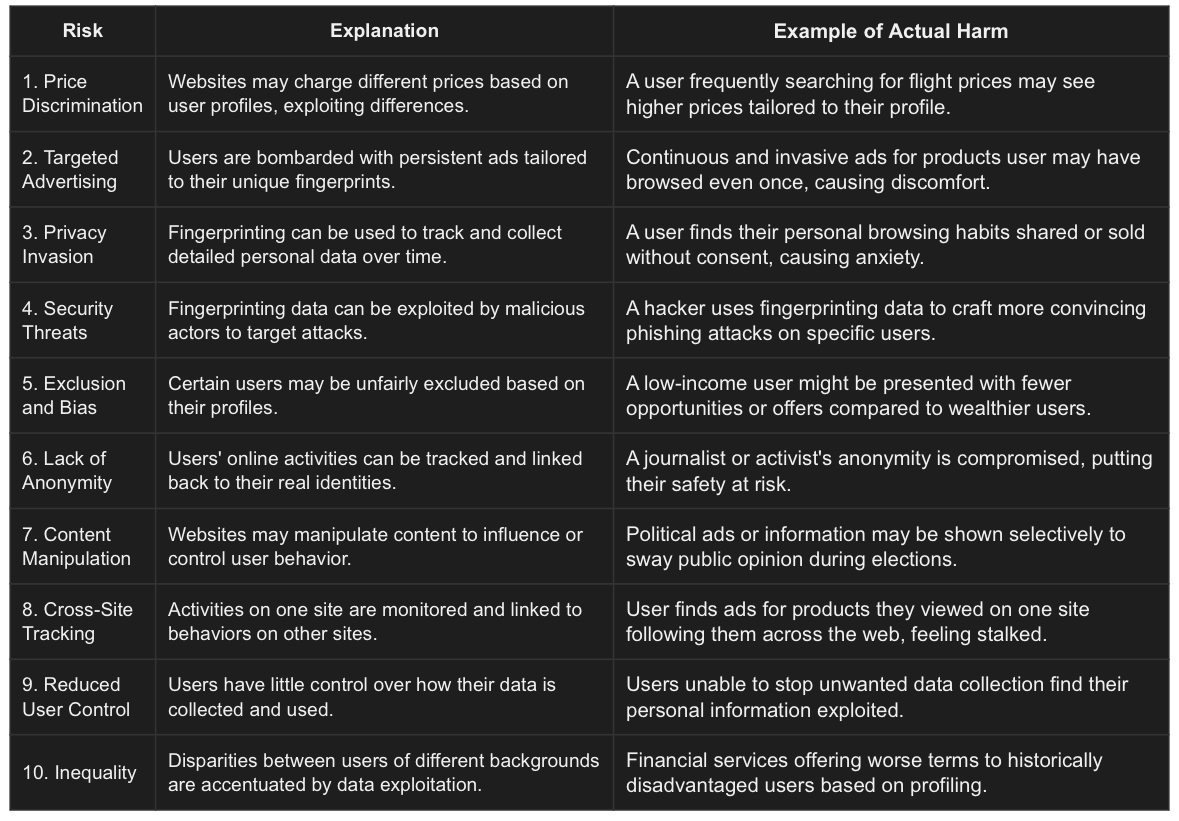
I worry about price discrimination
I appreciate the list. I’m not saying there aren’t valid concerns, just that in my day to day life it’s one of those items where the steps needed to avoid browser fingerprinting is usually more work than the value I personally get from my perspective.
I’ve looked into this, and I’m not clueless. I’ve developed websites, I’ve done a lot of stuff with Selenium / Puppeteer, and have toyed with Firefox browser extensions.
I understand the tools they use and it’s just very tricky to fully eliminate this type of thing. For example they can even use the browser window size. Are you going to randomly change window size to some novel dimension when you open up a tab?
What about the JS engine you use. For example using Firefox already narrows down your anonymity by like 95% or something because only a small amount of users use the browser. Etc etc
It’s hard to do this correctly, and I feel like VPN + private window usually takes care of the price fixing thing on the list, for example. When I’m searching for flights I usually do this.
I also use JS blockers in order to try and mess up the scripts that Facebook & Google have hidden over the internet to track you. But ironically, doing that again reduces your anonymity. They know that if their scripts don’t work on you, you get narrowed down again to a very small % of users.
It only takes a few of those pieces of data to be reasonably sure that it’s you. Browser fingerprinting is tricky to really avoid. It’s not impossible, of course. Just saying to really do it right it might be more effort than it’s worth.
The depth of fingerprinting really bothers me and I have accepted that the best at it will succeed.
It is tempting to find the world’s most popular default configuration and use that :) But that’s prob be something gross like Windows 10 & Chrome! In fact, that’d be second after Android & Chrome. Wonder how detectable VMing/emulating those configurations would be.
Agree with you and appreciate the detailed response!
deleted by creator
No. If you don’t want to be tracked and you are using a VPN, fingerprinting is a problem as well. Privacy is not concern just for drug dealers.
Became? 🤔
Torrenting itself is not illegal. The distribution of copyrighted material that you don’t own is the illegal part.
Different places have different laws
It’s sort of legally gray but generally speaking in the US downloading is a civil offense but not a criminal one. You can get sued by the copyright holder for example but you won’t end up in jail over it.
People usually never get sued for it because it’s not worth it for Comcast to pay for lawyers to try and extract any money out of regular people. Not only will they almost certainly be unable to even recoup the lawyer fees, they risk getting a lot of bad PR for no gain.
What’s usually considered an arrestable offense is uploading aka distribution. Once you start hosting seedboxes then you enter the area where you’re liable to go to prison.
Switching from Firefox to Librewolf has some pros and cons. Librewolf is a fork of Firefox focused on privacy and security, with telemetry stripped out and privacy settings maxed out by default. You’ll gain better out-of-the-box privacy protections, meaning less tracking and data collection without having to tweak settings yourself.
However, you might lose some convenience. Librewolf might not support certain Firefox features like Sync, since it relies on Mozilla’s servers (not sure about that point, maybe it does work). It can also break some websites due to the stricter privacy settings. Another thing to consider is that you won’t get updates as quickly as Firefox.
Regarding browser fingerprinting, it’s a tricky beast. Librewolf can help somewhat by making your fingerprint less unique, but it’s not a silver bullet. Tools like uBlock Origin and container tabs are great, but adding something like the CanvasBlocker extension can also help reduce fingerprinting. Ultimately, no setup is perfect, but Librewolf is a solid step towards better privacy.
I don’t really care too too much about privacy. If they get rid of the Pocket button then I’d be happy enough.
About:config
Extensions.pocket.enabled false

May I please steal this for future use?
I stole it too lol
Firefox sync is disabled by default but you can enable it in the settings.
Yes, why to do this?
Mostly it’s just FF but with more private defaults (that you can change in the settings trivially anyway), although there are one or two extras.
There is a potential issue, though. Librewolf runs behind, so security vulnerabilities, particularly for zero-day exploits, take longer to be patched.
if it’s fingerprinting you care about, i’d give mullvad browser a try. it’s a firefox fork tailored to increase privacy and blend you into the crowd (as long as you don’t change any setting/install addons). it’s very very neat.
Would everyone who is surprised by this please raise your hand? . . . That’s what I thought.
I am
License and registration, sir
Really? That’s not what the data from your api says /s
You don’t need to actually write it, just raise your hand and we have registered your vote, either via your computer’s camera, Google Nest, Google Assistant or inferred it by analysing the WiFi data returned by your Google Mesh network.
Keep your hand raised because I’m coming in for a perfectly-landed high-five!
perfectly-landed never happened before, and never will
Not surprised, but still disappointed.
It baffles me that they sell Chrome as private and/or secure, and baffles me even more that people believe them.
It baffles me people use chrome.
Why? There was a time when chrome was significantly better, and most people hate change.
I remember back in the day everyone used Firefox. Then Chrome came out and there was a nice ad campaign and it was actually way faster.
Then slowly everyone switched to Chrome. At some point in the last 15 years, it switched to Firefox being superior.
I switched back to Firefox maybe like 7~ years ago? But I did it for open source reasons.
This is hilarious! It even works on Edge, Vivaldi and even Brave 🤣. Good thing I use Firefox in almost everything or general day to day use
Firefox 🔛 🔝
🦊🦊
Vivaldi and Brave have the option to disable the Hangouts extension in settings, which should disable this.
As linked in the article, it is indeed used for “Hangouts” (Meet) troubleshooting.
This is good news since Vivaldi is my goto chromium browser (when I need to really use it)
I’ll admit, in several places I used Edge as an effort to have at least some layer of distrust between myself and Google. I’ll have to quit that though.
I like your style. I went looking and found “switchbar” which kinda/sorta eases this bouncing between browsers idea:
https://chromewebstore.google.com/detail/open-with-switchbar/klgpknafjlhnpkppfbihchgfebbdcomd
It’s not elegant, but it supports the workflow you suggest. I kind of like the idea of using Edge for google.com and Chrome for microsoft.com. I’m not optimizing my experience (it may in fact be very sub-optimal), but I’m also using competition to neutralize potential shenanigans.
I kind of like the idea of using Edge for google.com and Chrome for microsoft.com.
Dang, just use Firefox. It’s so much easier then this
such a sensationalist article there. mozilla isnt an advertising company, they bought a company that specialises in privacy focused ad campaigns so they can provide an alternative to google for companies.
which is what they should be doing.
Welp, might as well just use w3m 🤣
idk what to tell you if you’re still using chrome
Or anything Google for that matter. I see a lot of praise on Lemmy for their Pixel phones, but it wouldn’t surprise me if they eventually find there was a backdoor in their firmware all this time. Yes of course, I can not prove that right now, but this news about Google Chrome isn’t news for no reason. Don’t trust anything Google if you care about privacy, it is literally their business model (selling targeted ads).
Relevant username.
People don’t hate Google as much as they should. It’s cringeworthy how much they promote this ad company on this platform. They don’t even realze themselves they got comprised.
Wrll you have to use a pixel phone to use graphene os
Yeah, I’m not super happy about that part, but don’t really know what to do
Use a Pixel phone. No more sketchy then any other popular phone manufacturer
It’s what I do. With degoogled os. But the proprietary blobs aren’t filling me with confidence.
Does your laptop run free software boot firmware? If not, it has the same issues as a phone, if not more. No smartphone runs fully free firmware.
I know all this and that’s not filling me with confidence, either. It’s why Framework is in my sights.
Eat the ads then.
Well pretty much all computers have a backdoor to the CPU. That hasn’t been proven for Pixel phones though.
No, only Google has backdoors that are coming to light tome after time. Stop defending them Google ad fan boi.
Is this trolling or are you for real?
I fucking hate Google and wouldn’t use any of their (proprietary) software, but Pixel phones are amazing. Hear me out, Google is the only phone manufacturer right now, that puts extensive hardware security features like MTE, a secure element, as well as a bunch of others in their phones. The Google Titan M2 is based on an open-source project called OpenTitan, and Google has even contributed their own changes upstream. It’s based on the open RISC-V architecture, and it’s the most complete and secure implementation of a secure element that you can find in an Android phone. The only thing that comes even close is the “Secure Enclave” in Apple ARM chips, that are used in modern iPhones, iPads and Macs. I understand the concern about a potential backdoor in the firmware, but that’s a valid concern with basically every CPU on the market right now. x86 are ARM are completely proprietary, so you can’t really trust any CPU based on one of these architectures. The old Google Titan M1 was based on ARM, Apple’s Secure Enclave is also based on ARM, as well as Snapdragon’s SPU (which is incomplete and insecure anyway). The Titan M2, being based on open hardware architecture and firmware, is the most trustworthy secure element, despite being made by Google. It includes features like Insider Attack Resistance, support for the Weaver API, Android StrongBox hardware keystore implementation and is used for a secure implementation of Android Verified Boot. GrapheneOS is free, open-source, and doesn’t use any proprietary Google apps/services by default. Although I hate Google, a Pixel with GrapheneOS is currently the best option for a secure smartphone.
Google fan boy. Good luck promoting that shitty ad company.
Ah yes, definitely promoting Google
I fucking hate Google and wouldn’t use any of their (proprietary) software
I hope you realize how dumb your comment is
I do: DON’T
#UninstallChrome
#SwitchToFirefox
Here, you forgot this:
\
Remember when Google pushed for use of open standard in the browser to force Microsoft IE out of the market? Oh yeah I ‘member
They have become the evil they once sought to combat.
If you’re still using Google Chrome in 2024, you might be a moron. #Firefox
I am “slightly” worried that there’s only a single option left. That’s only 1 organization’s corruption removed from total loss of control over browsing privacy :/
And Mozilla main source of income is… Google.
This is bad, very bad.
Google pays them to be the default search. FF is like Steve Irwin, you could have been the biggest poacher, if you gave him money he would use it to buy land to help protect animals. FF is pulling the same thing but for the intetnet
so donate and change that
There’s safari and pale moon
Google does a lot of standards breaking things.
Like allowing a link on Google Apps Marketplace to open a new window (like popup) with POST instead of GET. (This pretty much ensures that buying an app will fail for browsers that follow the spec)
This garbage behavior is in Chromium as well?
There’s a bunch of stuff in Chrome that’s special-cased to only allow Google to access it.
Not sure if it’s still there, but many years ago I was trying to figure out how to do something that some Google webapp was doing (can’t remember which one). I think it was something to do with popping up a chromeless window - that is, a new window with no address bar or browser chrome, just some HTML content.
Turns out the Chromium codebase had a hard-coded allowlist that only allowed
*.google.comto use the API!Edit: my memory was a bit wrong. It was this: https://stackoverflow.com/a/11614605. The Hangouts extension was allowlisted to use the functionality, but if any other extension wanted to use it, the user had to enable an experimental setting.
Are you talking about the “apps” that Chrome used to support? They removed the feature years ago to reduce bloat and RAM usage or something like that.
Before they removed the feature, I had actually figured out how to create my own “apps” that’d simply load webpages I visited often at the time, like Twitch.
I don’t know why, but my head automatically put that as “the apps formerly support by Google” the same as “the artist formerly known as Prince”
I found what I was talking about: https://stackoverflow.com/a/11614605. It was a feature that the Hangouts extension could use, but the user had to manually enable it in the browser settings for any other extensions to use it.
The apps feature is still there just with a different name. It’s labeled as “create shortcut”, and you have to check the box to open a new window. I use it just because Firefox doesn’t have a similar feature.
How long until it will be used as a backdoor to hack womeone’s PC?
Chrome is the backdoor and you already installed it
Seems google has already done that
Negative number.
Ianal, but this sounds like something worthy of suing their ass over. There’s not much Google would respond to and good luck beating their lawyers, but the only language they speak is $, so please try to take as much as possible away from them for this garbage.
Not a legal mastermind by a long shot but it seems like a DMA violation. Someone needs to get the EU on their ass.
EU: [RELEASES THE HOUNDS]
Just make sure it isn’t the Pomeranians this time
Make sure it isn’t just the Pomeranians. Some Pomeranians are definitely going to be in the mix.
Ok, I’m good with that.
I had to look up what the Pomeranian dog breed is, because I’m not good with dog breeds. Soon as the page of images loaded I burst out laughing. 😆 Thank you. Good start to my day.
Glad to help. 😁 Get out there with that little dog energy.
lmao is been good so far. Have to make a long trip with the kids today, so it helped. ❤️
Hmmm, no way this could ever turn into a security hole, I’m sure of it.
I already ditched Windows for Linux a month ago because of spyware. Everything Google-related is next. My phone is going to be the hardest thing to de-infest.
In my experience you either have to trade one devil for the other with Apple or accept buying hardware from the ad company so you can use GrapheneOS.
There are more options than GrapheneOS with broader device support, such as Calyx or LineageOS.
But if you use Android already, you can start by using F-Droid (or others) to install apps to find FOSS replacements for apps you use.
Searching for “Calyx” got me a lot of results that had nothing to do with the Android ROM, so for the convenience of anyone else reading this thread their URL is https://calyxos.org/
Thank you
You could always go the used/refurbished route to not directly give the chocolate factory money
I already ditched Windows for Linux a month ago because of spyware.
Great!
Everything Google-related is next.
Even better.
My phone is going to be the hardest thing to de-infest.
If you plan on getting a new phone soon, I recommend a Google Pixel, on which you can install GrapheneOS. Yes, ironically Google devices are the best for installing alternative operating systems and removing all the Google BS. GrapheneOS is completely free and open source, and based on the Android Open Source Project. It incorporates many privacy and security enhancements, and gives you total freedom and control over your device. In my opinion, it’s the best option for degoogling a phone.
There is also Lineage OS. It’s not as secure but it is compatible with the most amount of devices.
Unfortunately LineageOS is highly insecure because there’s no ability to lock the bootloader, and Android Verified Boot is completely missing. These are just the biggest and most obvious flaws in Lineage, but there are more: https://madaidans-insecurities.github.io/android.html#lineageos
Android is a very secure system, but that comes with some compromises such as customizability and development features. Both of which are important to the Lineage OS project. Also running Lineage OS is not any more insecure then running a Linux or Windows desktop without secure boot, which many people do without issue
I kinda want to, but I’m also a sucker for ease of use
For ease of use Apple might be the most convenient alternative to Google. At least for smartphones.
Ease of use and apple are not near each other in my dictionary.
I think a lot of things are designed very unlogical
That might be because you are just not used to it. Comparable to the switch from Windows to Linux.
I’m using Linux and tried different distros. I also used chrome os and windows Phone. I tried ios, hence my feelings towards it
And many people tried Linux and were having difficulties adapting to it at first and most probably gave up. Just like you did with iOS.
Pff, sure buddy. Used it for 4 months due to my phone being dead. Go shill someone else. If the adoption of a new os goes against what I want of said os, then it’s not an os for me. Simple as that
Kagi is a great replacement for Google search. It does cost money though.
Or you can take a Duck. Then get one more Duck. Then you can Go.
Welcome to the world of freedom. The first months may be a bit uncomfortable, but it’s a journey worth taking. Be welcome!
I’m also doing this. Proton is amazing, for the most part. Ente Photos is also incredible for ditching Google Photos, although I’ll probably switch to Proton Photos when that comes out since Ente is pricey.
Isn’t proton photos built into their Proton Drive already? It’s implementation is… barebones… On Android but it works.
It is, but I’d barely consider it a launch of anything. It displays photos, but that’s it. I could already upload and view photos on Proton Drive before they “launched” this.
Or if you have the skills you can selfhost Immich which is an excellent replacement for Google Photos.
Honestly I just keep my phone as my designated privacy nightmare so I can get free phone calls on wifi and keep in touch with family members who are still on facebook.