Why YSK: Websites on the internet often try to uniquely identify your device, this extension attempts to prevent that and make it hard for them to do so.
Firefox’s built in “Enhanced Tracking Protection” already does a lot of this work for you, especially if you select “strict mode.” Go ahead and try this extension if you prefer. But remember to be selective with the extensions you add to your browser in general, as they also present an opportunity to introduce vulnerabilities.
I tried that and then one of those “how common is your fingerprint” websites said my fingerprint was unique. Literally fucking unique.
I think it was the EFF site.
Might have something to do with other extensions I have installed like Canvas Blocker, uMatrix, etc.
Fuck, even in Mull on my phone where I only have a few extentions installed: uBlock Origin, cookie auto delete, local CDN, and a cookie consent blocker.
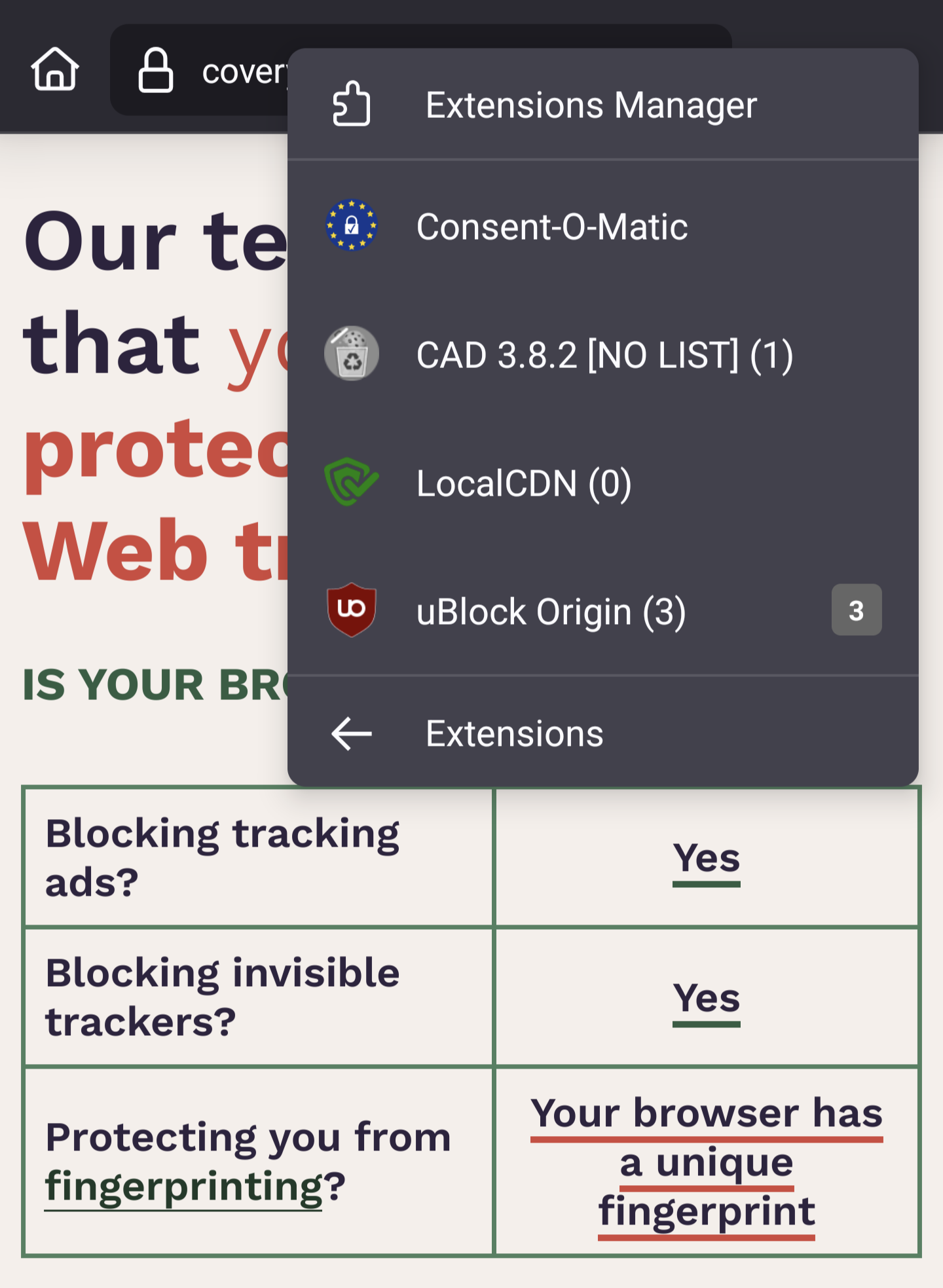
As you suggested, I suspect it’s the rare combination of additional extensions that’s contributing to your uniqueness in a fingerprinting sense.
I tried turning them all off and nothing changed. Same result with the Duck Duck Go browser set on Android. Unique fingerprint. And I have no extensions. I wonder if my VPN is part of the fingerprint. I did read a lot of the explanation of what fingerprints you, but I didn’t see VPN in there. I should do a search on that page to see.
He could explain it but every time he does he ends up proving our point.
I’m not sure what you mean?
I was replying to a different post.
I have never seen this post before just meow. No idea how it got this borked.
How do I know it’s actually safe to install? Lol
Prolly just a trust me bro that some smart coder chad did the dilligance
That’s a lot better than closed source, which is just “trust me bro”.
I dont disagree but didnt check the code… I trust the bro🫡
You’re asking the right questions! @[email protected] has the right answer
It’s the right answer if you know how to read code
The only alternative is closed-source, which is just “trust me bro”. At least with open-source you have the option to check it for yourself. Doesn’t have to be a perfect system
I figure if it’s open source someone will have read the code and I can settle for riding that effort
That let me sleep easy for twenty Years. Then xz happended. I am uneasy now.
It’s open source. You can compile from source.
In addition to the code being freely available, as others have pointed out, the developer has attended some number of software conferences at which his knowledge of this subject matter and this project makes itself evident.
What’s so funny that had you loling?
They’re just saying it in a jovial, not so serious tone lol. Maybe you should lighten up lol
It’s open source, you can take a look here: https://pagure.io/JShelter/webextension
LOVE jShelter. Use it on all my devices (woooo mobile firefox addon compatibility!!).
It is an EYE OPENER to see all the websites that will refuse to serve you when they can’t identity exactly who you are…
It breaks Cloudflare so for me tons of websites become inaccessible. Maybe you can tweak it but OOTB it’s unusable
What I like is that JShelter doesn’t try to “hide in the crowd” with its spoofed attributes which is IMO a failing strategy as the crowd increasingly becomes atomized by adtech.
Yeah i get this approach theoretically but i dont think it works but that just a normie opinion.
Like why would not i add privacy badger on top of ublock since ublock passes some stuff like google login pop ups?
The approach once worked, but that was back before browsers began including the likes of things like advertiser IDs and other extremely high entropy attributes that no average person would ever think to disable. Contemporary hide-in-the-crowd strategies are mostly curated within efforts like Tor browser where everyone is encouraged to use the exact same configuration. But then it’s still a numbers problem. If only two attendees decide to hide their faces with party masks to a soiree of 100 people, one (large scale observer) only need check the guest list and use process of elimination to determine the identities of the 2% “hidden” attendees.
Somebody can, and probably will, come along and refute this assessment. I am not entirely convinced myself that it is a losing strategy yet. I’m open to hear opposing takes.
Privacy Badger:
IIRC Privacy Badger operates by logging third party domains connections on a per-site bases, and only begins to actively block connections once a domain seen across multiple visits fits the profile of a likely tracker.Nvrmnd, they’ve changed how PB works and it is now closer to a list-based tracker blocker (enumerate badness):
So they’ve since corrected one of the core issues with PB. Still it is weak. To see why, please glance through The Six Dumbest Ideas in Computer Security.
uBlock Origin in advanced mode, with default-deny rules (only allow assets by exception) is going to be much stronger at blocking crap.
Personally, I use uMatrix with pretty much all asset classes blocked by default. I never see popups. I never see banners begging “please allow our cookies, pleeeeaaase!”.